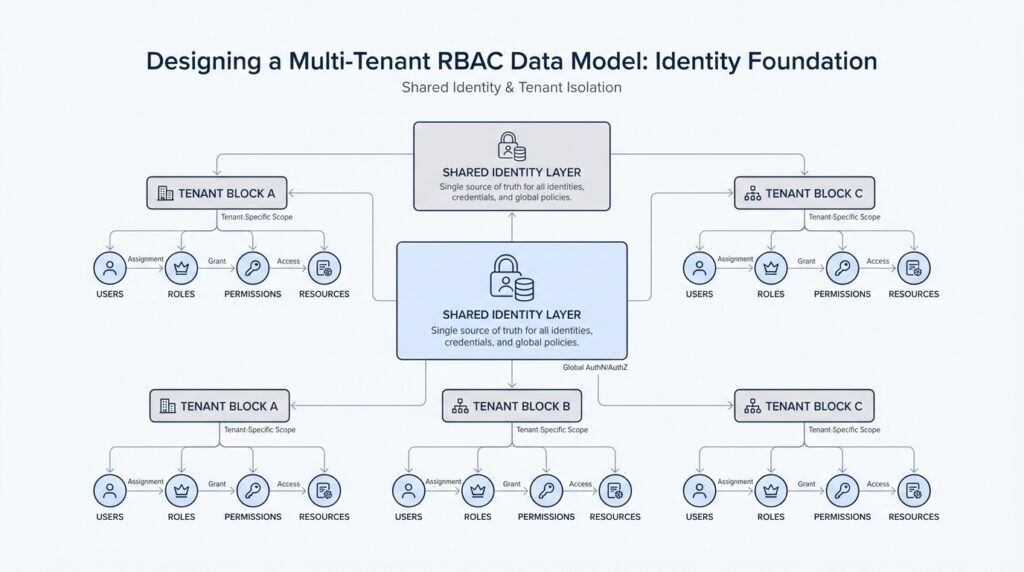
Define Tenant Identity Boundaries
Building on this foundation, the next question is the one that quietly shapes everything else: how do you keep one customer’s access from bleeding into another’s? In a multi-tenant RBAC data model, the answer starts with tenant identity boundaries, which means we draw a clear line around which identities belong to which tenant and which permissions can ever apply there. Think of it like an apartment building with separate mailboxes, keys, and door codes. If the lines are blurry, the whole building feels unsafe.
A tenant is one customer, organization, or workspace inside a shared application. Identity, in this setting, is the information that proves who a user, service, or device is. When we talk about identity boundaries, we mean the rules that decide where that identity can exist, what data it can touch, and which role-based access control decisions can use it. Role-based access control, or RBAC, is the system that grants access based on roles such as admin, manager, or viewer rather than on one-off exceptions.
This is where the multi-tenant RBAC data model starts to feel real. If you let every user live in one global identity pool with no tenant context, you create confusion fast: the same email address might belong to two different customers, or an admin role in one company might accidentally look valid in another. By defining tenant identity boundaries early, you make it possible to say, “This person is a user here, and only here,” or “This service account belongs to this workspace, not that one.” That separation is the identity foundation everything else depends on.
How do you actually define those boundaries in practice? We usually start by attaching a tenant identifier to every identity record and every access decision. That tenant identifier acts like a passport stamp, telling the system where the identity came from and where it is allowed to operate. Once that stamp exists, roles can be evaluated inside the tenant context instead of across the whole platform, which keeps permissions local and predictable.
Now the story gets more interesting, because boundaries are not only about users. They also apply to groups, service accounts, invitations, and even the roles themselves. A group called “Finance” in one tenant should never be treated as the same group in another tenant, even if the names match. The same idea applies to an invitation link or an API token: if it is not clearly tied to a tenant, it can become a shortcut around your security model.
This is why careful tenant identity boundaries help both security and simplicity at the same time. Security improves because data and permissions stay contained, so one customer cannot accidentally see another customer’s records. Simplicity improves because your application can make cleaner decisions: first identify the tenant, then load the identities for that tenant, then evaluate roles within that space. That sequence keeps the multi-tenant RBAC data model understandable, especially when you later add more complex rules like delegation or nested teams.
There is also a practical benefit when users belong to more than one tenant. A consultant, for example, might work with three different client organizations in the same product. Instead of treating that person as one floating identity with universal access, we treat them as a shared human with separate tenant-scoped memberships. That distinction preserves flexibility without weakening the tenant identity boundaries, which is exactly what you want when a single login needs to wear different hats in different places.
Once these boundaries are clear, the rest of the system becomes easier to reason about. You can ask better questions, like which identities should be created per tenant, which should be global, and which permissions must never cross the line. That clarity gives us a stable identity foundation for the next step, where we start mapping roles, memberships, and access rules onto those tenant-scoped identities.
Model Users and Tenants
Building on this foundation, we now have to give the people in the system a shape that matches the boundaries we already drew. In a multi-tenant RBAC data model, the biggest mistake is treating every user like a free-floating account with no home. Instead, we model a user as the person or service identity itself, and we model a tenant as the place where that identity is allowed to operate. That sounds small, but it is the difference between a clean identity foundation and a system that becomes confusing the moment the second customer signs up.
The first question is usually, how do you model a user who belongs to two customers at once? The answer is to separate the human from the membership. A single user record can represent the person, while a tenant membership record says how that person relates to one specific tenant. Think of it like having one passport and several visas: the passport is the person, but each visa says where they can enter and what they can do there. This pattern keeps the multi-tenant RBAC data model flexible without pretending that every relationship is the same.
That separation also helps us avoid a common trap: duplicating the same user over and over for each tenant. If you create a brand-new user row every time someone joins a workspace, you may make the data look simple at first, but you lose the ability to see that it is the same person across different places. A cleaner design gives the user a stable identity and attaches tenant-scoped details where they belong. Those details might include display name, invitation status, or local preferences, but the core identity stays consistent.
Now that we have the pieces, it helps to name them clearly. The user is the account that can sign in. The tenant is the organization or workspace that owns a slice of the application. The membership is the join between them, and that join is where roles usually live. This is where the identity foundation becomes practical, because RBAC does not answer the question of who a person is; it answers the question of what that person can do inside a specific tenant.
When you separate users and tenants this way, role assignment becomes much easier to reason about. A person can be an admin in one tenant and a viewer in another without any conflict, because the role belongs to the membership, not the person globally. That is one of the quiet strengths of a multi-tenant RBAC data model: the same login can wear different hats depending on the tenant context. Without that distinction, you end up either over-granting access or creating awkward special cases that are hard to maintain.
This model also makes onboarding and invitations feel more natural. A tenant can invite a user before that person has a full membership, and the system can store the invitation as a tenant-scoped object until it is accepted. Once the user joins, the invitation turns into a real membership, and the tenant can safely attach roles to it. Here again, the tenant boundary does the heavy lifting, because every action has a clear owner and a clear scope.
As we discussed earlier, tenant identity boundaries protect both security and clarity. Modeling users and tenants with a separate membership layer extends that idea into the database itself, where the relationships need to be precise enough for the application to trust them. If you get this part right, later work becomes much smoother, because roles, groups, and permissions can all build on a structure that already knows who belongs where. That is the kind of identity foundation that makes the rest of the design feel steady instead of improvised.
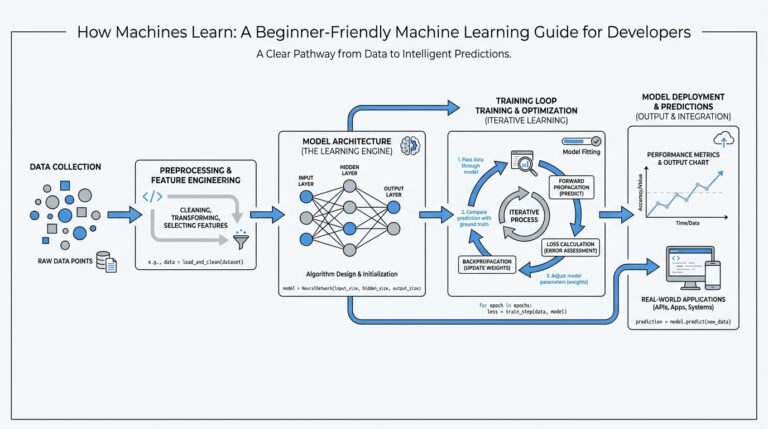
Map Roles to Permissions
Building on this foundation, we can finally answer the question that turns names like admin and viewer into real behavior: how do you map roles to permissions in a multi-tenant RBAC data model? This is the moment where the system stops feeling abstract and starts acting like a set of working rules. A role is the label people understand, while a permission is the exact action the software allows, like reading an invoice, editing a project, or inviting another member. Think of the role as the recipe name and the permissions as the ingredients and steps that make the dish possible.
That separation matters because roles are meant to stay human-friendly, while permissions need to stay precise. If we only store roles, we know someone is an admin, but we still do not know what that means in practice. If we only store permissions, we get exact control, but we lose the simplicity that makes access rules easy to manage. In a multi-tenant RBAC data model, the clean pattern is to define permissions as atomic actions and then attach those actions to roles inside the tenant’s own scope.
How do you turn an admin role into concrete access rules? You start by treating permissions like small building blocks instead of giant bundles of power. A permission might say project:read, project:update, or member:invite, and a role becomes a curated collection of those actions. That way, an Editor role can share some permissions with an Admin role without becoming identical to it, and a Viewer role can stay safely limited to read-only access. This is where RBAC becomes practical, because the database can answer a simple question: what can this role do here?
The tenant context still matters at every step. A role called Manager in one tenant should not silently inherit the same permission set in another tenant, because each customer may define the role differently. One tenant might let managers approve invoices, while another only lets them view reports and assign tasks. In a multi-tenant RBAC data model, the role-to-permission mapping belongs to the tenant, not to the whole application, so each organization gets its own version of the same idea without cross-tenant leakage.
This is also where custom roles become useful. Many teams start with a few standard roles, but later they need a role that sits between two existing ones, such as Billing Manager or Support Lead. Instead of hardcoding those cases, we let tenants compose their own roles from the permission catalog we already defined. That gives you flexibility without chaos, because the application still evaluates the same underlying permission names even when the role labels differ from tenant to tenant.
A helpful way to picture the structure is to imagine a library card system. The permission is the individual right to check out a certain kind of book, while the role is the membership tier that bundles several rights together. The same person may hold a basic card in one branch and a premium card in another, but the checkout rules still depend on the local branch’s policy. That same idea carries into the multi-tenant RBAC data model: the membership decides which tenant context applies, the role picks the bundle, and the permissions decide the exact action.
Once these mappings are in place, the rest of the authorization flow becomes much easier to trust. The application can load the user’s tenant membership, find the assigned role, and expand that role into a clear set of allowed permissions before checking any request. That gives you a system that is both readable for humans and predictable for software, which is exactly what we want before we move on to how those checks are stored, queried, and enforced.
Bind Identities at Signup
Building on this foundation, the next moment that matters is the one where a person first enters your product and becomes more than a visitor. At signup, we are not only creating an account; we are binding that identity to a tenant so the system knows where it belongs from the very first request. In a multi-tenant RBAC data model, that early decision keeps later access checks clean, because the application does not need to guess whether the person is still unassigned, already invited, or meant for a different workspace.
How do you bind identities at signup without making the process feel heavy? The key is to treat signup as the point where the system records both the person and their first tenant-scoped membership. A signup is the moment a user creates an account or accepts an invitation for the first time, and binding means attaching that account to a specific tenant context right away. Think of it like handing someone a visitor badge at the front desk instead of letting them wander the building and figure out their own door access later. The badge does not change who they are; it tells the building where they are allowed to go.
This is where the identity foundation starts doing real work. If a customer signs up to create a new workspace, the application can generate the tenant and then create the membership in the same flow. If the person is joining an existing tenant through an invitation, the system can convert that invitation into a live membership instead of treating the person as an unplaced account. In both cases, the result is the same: the identity is bound at signup, and every later role assignment has a clear home. That is what makes a multi-tenant RBAC data model feel dependable instead of improvised.
A good signup flow also needs to answer a subtle question: is this identity global, tenant-scoped, or both? The answer depends on your product, but the pattern stays familiar. The user record usually holds the stable account information, such as login credentials or contact details, while the tenant membership record holds the relationship that matters for authorization. By separating those layers at signup, you can let one human belong to multiple tenants without merging their access into a single confused profile. That separation is especially important when you later support consultants, agencies, or administrators who move between workspaces during the day.
This early binding also prevents a common source of messy authorization logic. Without it, the system may have to create temporary access states, guess which tenant to load, or search across multiple membership records every time the user lands on a page. Once the identity is tied to a tenant at signup, the application can make a much simpler promise: identify the tenant first, load the matching membership, and only then evaluate roles and permissions. That sequence is one of the quiet strengths of a well-designed multi-tenant RBAC data model, because it reduces ambiguity before it becomes a security problem.
Now the story gets more interesting when signup is not the same as first payment, first project, or first login. You may want a person to register before they fully join a tenant, or you may want them to accept an invite before any access is granted. Even then, the same idea applies: keep the identity linked to a specific tenant state, even if that state is pending, invited, or active. What causes trouble is not the delay itself; it is allowing an identity to float around without a tenant context while the system tries to decide what it means.
Once you bind identities at signup, the rest of the journey becomes easier to explain and easier to trust. The user knows which workspace they entered, the tenant knows which members belong to it, and the authorization layer knows exactly where roles should be evaluated. That clarity is what turns onboarding into a secure starting line rather than a guessing game. And with that in place, we can move from identity creation into the next layer of the model, where those newly bound memberships start taking on real permissions and responsibilities.
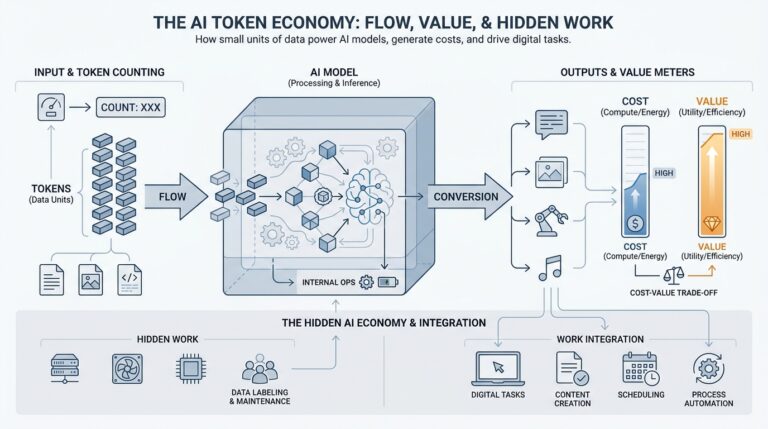
Store Tenant Claims Securely
Building on this foundation, the next problem is not who the user is, but how we keep the tenant claims attached to that identity safe once they exist. Tenant claims are the small pieces of data that describe a user’s tenant-specific context, such as a tenant identifier, membership identifier, or role name. In a multi-tenant RBAC data model, those claims guide every authorization decision, so storing them securely matters as much as defining them correctly. If they leak, get modified, or drift out of sync, the whole access story starts to wobble.
How do you store tenant claims securely when the same person may belong to several tenants? The first rule is to keep the claims minimal. Think of a claim like a luggage tag: it should tell the system where the bag belongs, not carry the entire contents of the suitcase. That means we usually store only what the application needs to make a decision, such as tenant_id, membership_id, and a role label, while leaving the heavier details in a trusted database lookup on the server.
This is where tokens and sessions enter the story. A token is a compact package of identity data, and a session is a server-side record that remembers who the user is across requests. If you use a signed token, the signature acts like a tamper-evident seal, telling you whether someone changed the contents after it was issued. If the claims are especially sensitive, a server-side session is often the safer place to keep them, because the browser only holds an opaque reference instead of the full access picture.
The main danger is trusting client-side storage too much. Anything stored in a browser can be copied, inspected, or replayed if the surrounding protections are weak, so tenant claims should never become a free pass to access data. That is why secure storage is only the first layer of defense; every request still needs server-side validation against the current tenant context. In a multi-tenant RBAC data model, the server should confirm that the claim matches the authenticated user, the active tenant, and the membership record before it allows access.
Now the design starts to feel practical. Store the claims in a place that matches their sensitivity, protect them with encryption when they need confidentiality, and sign them when you need proof they were not altered. Encryption means scrambling data so only someone with the key can read it, while signing means attaching a verifiable proof that the data has not changed. Those are different tools with different jobs, and using them correctly helps keep tenant claims secure without making the system hard to work with.
You also want claims to age out quickly enough to stay trustworthy. If a user’s role changes, a tenant membership is removed, or an invitation is revoked, stale claims can keep granting access longer than they should. That is why expiration, refresh, and revalidation matter in the multi-tenant RBAC data model. A short-lived claim reduces risk, and a fresh server-side check keeps the application aligned with the latest tenant state instead of yesterday’s version of reality.
There is a subtle but important pattern here: store the claim, but do not let the claim become the source of truth. The source of truth should remain the database record that defines the membership, tenant, and role relationship. The claim is a convenient snapshot, useful for speed and context, but it should always be checked against the tenant boundary we defined earlier. That is how secure storage supports authorization instead of quietly replacing it.
With that in place, the system gains a calm, dependable rhythm. The user signs in, the application loads the tenant claims from a protected place, and the server verifies those claims before evaluating access. That rhythm keeps the multi-tenant RBAC data model stable, even when people belong to more than one tenant or when roles change over time. And once you have that trust boundary, the next step is to decide how those claims travel through requests without exposing more than they should.
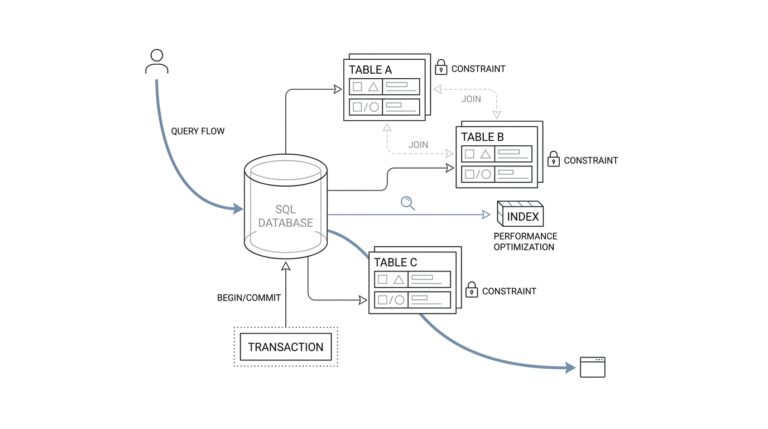
Enforce Cross-Tenant Checks
Building on this foundation, the next safeguard is the one that keeps a valid identity from reaching the wrong workspace. Cross-tenant checks are the guardrails that compare a user’s active tenant, their membership, and the resource they are trying to touch before any action is allowed. In a multi-tenant RBAC data model, this is where the design stops being about stored data and starts being about real protection. Without that check, a user may still look authenticated while quietly stepping over a boundary they should never cross.
How do you know a request belongs in the right tenant? You ask the system to prove it at the moment of use, not only at sign-in. That means every request should carry tenant context, and every server-side decision should verify that the claimed tenant matches the membership record and the target record. Think of it like checking both the ticket and the seat number at a concert: having a ticket matters, but it is not enough if it belongs to a different row.
This is where cross-tenant checks become more than a single if-statement. A request to view a project should confirm that the project belongs to the same tenant as the user’s membership, and a request to edit a billing setting should confirm the same thing before permissions are even evaluated. The authorization flow should look like this: identify the tenant, load the membership, confirm the resource owner, then expand the role into permissions. That order keeps the multi-tenant RBAC data model honest, because no permission can act on a resource that lives outside its tenant boundary.
The safest place for these checks is the server, not the browser. A client can display the right tenant name, but the server must make the final call because it owns the source of truth. This matters even more when users belong to several tenants, because a person who is allowed to manage one workspace may also be a guest in another. Cross-tenant checks prevent that mixed identity from becoming mixed access, which is one of the most common ways multi-tenant systems leak data.
One useful pattern is to enforce the tenant match in every data lookup. Instead of asking for “project 42” alone, the application should ask for “project 42 in tenant A,” so the query itself becomes part of the security model. That extra context acts like a locked address label: even if someone knows a record ID, they still cannot reach a record that lives under a different tenant. When people ask, “Why does my app still need authorization if the record ID is secret?” this is the reason—IDs are not boundaries, but tenant checks are.
Cross-tenant checks also need to cover indirect paths, not only obvious ones. Invitations, shared links, background jobs, and admin tools can all become shortcuts if they skip tenant validation. A support operator, for example, may have broad internal privileges, but that does not mean every tool should ignore tenant scope. In a strong multi-tenant RBAC data model, even privileged actions should confirm which tenant is in view, because elevated access still needs a destination.
As we discussed earlier, tenant claims are useful snapshots, but they should never replace a live check against the database. That is especially important when roles change, memberships are revoked, or a user switches tenants during the same session. A stale claim may say the user still belongs somewhere they no longer do, but the cross-tenant check catches that mismatch before it turns into exposure. This is the quiet strength of a layered design: the claim gives you speed, and the server-side check gives you truth.
Taking this concept further, the best systems make tenant validation feel boring in the best possible way. Every access path uses the same rule, every query includes the same scope, and every permission check starts with the same tenant comparison. That consistency is what makes the multi-tenant RBAC data model dependable under pressure, because the application does not rely on memory or special cases. It relies on a repeatable check that keeps one customer’s space firmly separate from another’s, request after request.