Define Agent Objectives
Before a portfolio agent can think, trade, or explain itself, it needs a clear purpose. This is where the agent objectives come in: the small set of goals that tell a large language model what it should optimize for, what it should avoid, and how it should behave when the path ahead is messy. If you have ever tried to follow directions that sounded clever but lacked a destination, you already know the problem we are solving here.
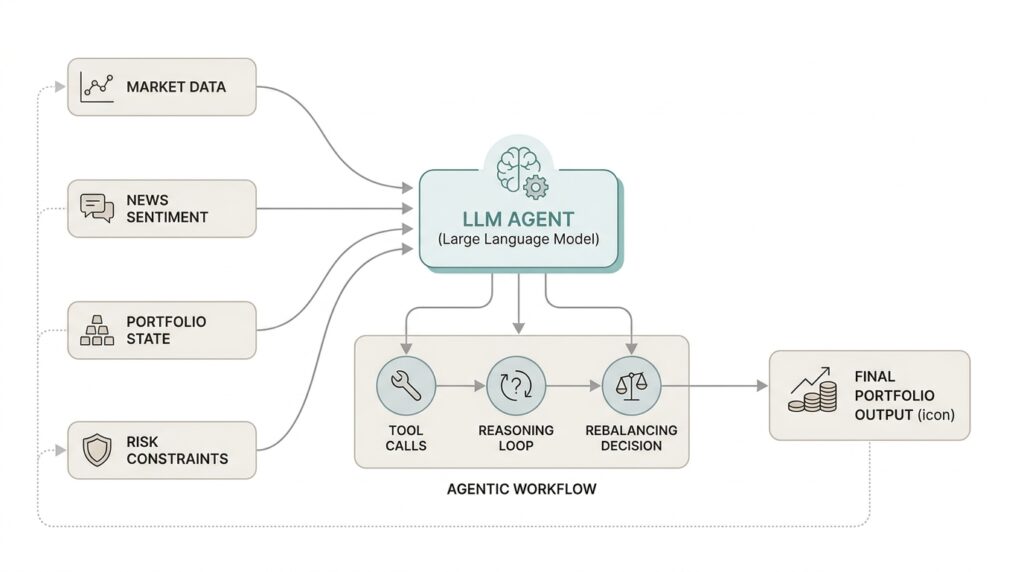
The first question is the one most people ask when they begin designing an agentic workflow: what should a portfolio agent actually do when markets move, data changes, or a user asks for help? We answer that by turning a vague ambition like “manage investments” into concrete objectives such as preserve capital, respect risk limits, stay aligned with user preferences, and respond with clear explanations. Each objective acts like a lane marker on the road, helping the large language model stay useful without wandering into guesswork.
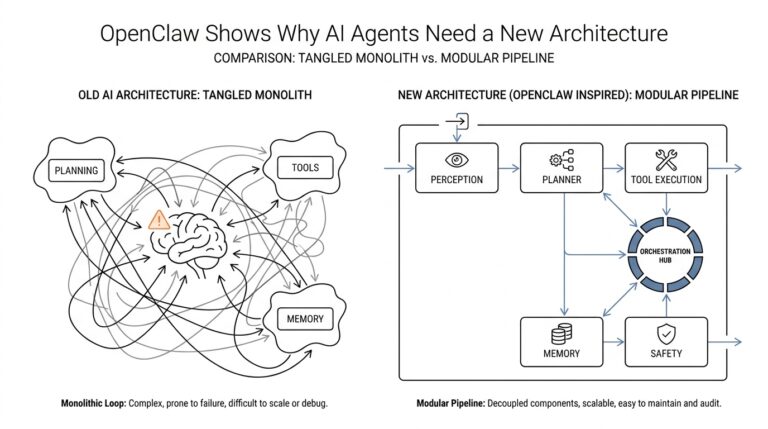
This step matters because large language models are excellent at generating language, but they do not automatically know what success looks like. In a portfolio agent, the objectives define that success in plain terms. One objective might focus on decision quality, another on safety, and another on communication, and together they shape the agentic workflow so the system knows when to recommend, when to wait, and when to ask for more information. Without that structure, the model can sound confident while still making choices that do not fit the user’s real situation.
A helpful way to think about agent objectives is to imagine a personal financial coach with a clipboard. The coach is not there to impress you with vocabulary; the coach is there to keep track of what matters, like how much risk you can tolerate, what time horizon you have, and whether a suggestion fits your goals. In the same way, a portfolio agent should treat objectives as the rules of the conversation and the boundaries of the decision process. That makes the system more predictable, easier to evaluate, and much easier to trust.
We also need to separate objectives from tactics, because these two ideas often blur together at first. An objective says what the agent is trying to achieve, while a tactic describes how it tries to get there. For example, “limit exposure to volatile assets” is an objective, while “rebalance monthly” is a tactic. Keeping that distinction clear helps us design an agentic workflow that can change methods without losing direction, which is especially important when the market environment shifts or the user’s needs evolve.
The best objectives are specific enough to guide action but broad enough to survive real-world complexity. A strong portfolio agent objective might sound like this: protect the user’s stated risk tolerance, surface trade-offs honestly, and avoid overconfident recommendations when the data is incomplete. Notice how this combines decision-making, communication, and restraint; those are all part of the job. When we define objectives this way, we give the large language model a map, not a script, and that makes the portfolio agent far more reliable in practice.
Once those objectives are in place, everything downstream becomes easier. The agent can judge which signals matter, decide whether it has enough evidence to respond, and explain its reasoning in a way that feels consistent from one interaction to the next. In other words, clear agent objectives do not just improve the portfolio agent; they make the entire agentic workflow feel coherent, so the rest of the system has something steady to build on.
Ingest Holdings Data
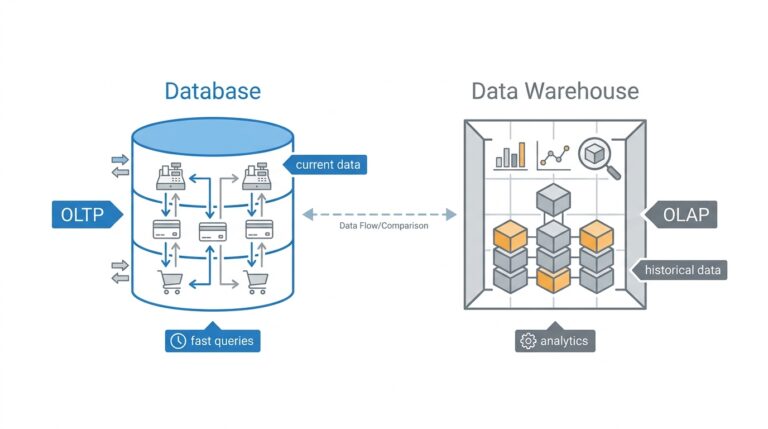
Once the objectives are clear, the next job is to bring the portfolio into the room. Ingest holdings data means taking raw position records and turning them into something the portfolio agent can actually reason about. What does that look like in practice? It means the system stops seeing a loose pile of numbers and starts seeing dated, named holdings with quantities, values, and identifiers that can be compared over time. The SEC’s Form N-PORT data model shows this shape well: each holding lives in a structured row, and related identifiers such as CUSIP, ISIN, ticker, balance, currency value, percentage, and asset category are captured in machine-readable fields.
The tricky part is that holdings data rarely arrives as a neat story from beginning to end. The SEC notes that N-PORT data is taken “as filed,” and that the published data may contain redundancies, inconsistencies, and discrepancies relative to prior submissions and other formats. That is exactly why ingestion matters: before the portfolio agent can think clearly, we need to protect the original record, inspect it, and then shape it into a cleaner working copy. In other words, raw data is the rough draft, and the ingested layer is the version we can trust to answer questions.
From there, we walk the data through a few quiet but important steps. Parsing means reading the file into fields the system can recognize, validation means checking whether required values are present and well formed, normalization means making different labels look alike inside the system, and reconciliation means checking whether two records agree when they should. The holdings table in N-PORT is already organized around this idea, with a main holding row and a separate identifiers table that can attach extra labels to the same security. That separation is useful because the portfolio agent can keep one internal record while still remembering every external name the asset has worn.
This is also where a security master comes in, which is just an internal catalog of the instruments the agent knows about. If one holding appears as a ticker in one place, a CUSIP in another, and an ISIN somewhere else, the security master gives us one consistent identity to hold onto. The N-PORT schema supports that reality directly: the holding table can store issuer name, issuer LEI, issuer CUSIP, and the identifiers table can add ISIN, ticker, or another identifier with a description. That design is a reminder that holdings data is not only about values; it is also about identity, and identity is what keeps the portfolio agent from double-counting or misreading the same asset.
Timing matters as much as structure. N-PORT is a monthly portfolio holdings report for funds other than money market funds, and the SEC’s data sets are disseminated quarterly, which means our ingestion pipeline has to preserve as-of dates and filing dates instead of flattening everything into one timeless snapshot. When a new file lands, the agent should know whether it is looking at a fresh position, an amended filing, or a later view of the same holding. If we keep that timeline intact, the portfolio agent can compare changes honestly, explain what moved, and avoid the very human mistake of treating yesterday’s positions as if they were still today’s truth.
Once the holdings layer is clean, the rest of the workflow starts to feel less mysterious. The agent can ask better questions, because it knows which numbers are current, which identifiers match, and which records still need review. That is the quiet payoff of good holdings ingestion: before the portfolio agent can reason, it needs a reliable map of what it owns, and the map has to be detailed enough to survive real-world messiness.
Wire Market Data Tools
Now that the portfolio agent knows what it owns, the next question is the one that makes the whole system feel alive: what is that portfolio worth right now, and how is the market treating it? That is where market data tools enter the story. They give the agent a live window into prices, moves, and trading conditions, so the system can move from a tidy inventory of holdings to a real-time view of risk and opportunity. Without that layer, the agent can describe the portfolio, but it cannot feel the market around it.
A market data tool is any connector that fetches market information the agent needs to think clearly. In plain language, that usually means a quote, which is the latest price for an asset; a bar, which is a grouped slice of price data over time such as one minute or one day; and volume, which tells us how many shares changed hands. These pieces may sound small, but together they act like the agent’s senses. When we wire market data tools into the workflow, we are not adding decoration; we are giving the model the evidence it needs to compare a holding’s current value, recent trend, and trading activity.
This step matters because holdings data and market data answer different questions. Holdings tell us what is in the portfolio, while market data tells us how the outside world is pricing it today. A position that looked calm at filing time can behave very differently after a gap in price, a sudden rally, or a sharp drop, and the portfolio agent needs to notice that change before it speaks with confidence. What is a portfolio agent supposed to do when the price feed is stale or the symbol does not match the holding record? The honest answer is that it should pause, verify, and avoid pretending that yesterday’s number is still current.
Wiring market data tools well is mostly about making the handoff clean. The agent should know which identifier to send, what timeframe it is asking for, and how to interpret the response when it comes back. That sounds technical, but the pattern is familiar: if you ask a librarian for a book, you need the right title or catalog number, not a vague description. In the same way, the portfolio agent should translate a holding into the symbol or instrument key the market data tool understands, then map the returned price back to the same security master record we built from ingestion. This is how the agent keeps one identity for the asset while pulling in fresh market context.
We also need the market data tools to behave like careful assistants, not enthusiastic guessers. Prices can be delayed, markets can be closed, and some assets do not trade continuously, so the agent should treat missing values as a signal, not a failure to be hidden. That means checking timestamps, confirming exchange hours, and validating whether the quote belongs to the correct trading day. When the workflow includes these checks, the portfolio agent becomes far less likely to mix a delayed quote with a live one or to mistake an illiquid security for a quiet one.
Once the wiring is in place, the benefits show up quickly. The agent can estimate current exposure, compare cost basis with market value, and explain why a position looks larger or smaller than it did in the holdings file. It can also use market data tools to support more nuanced questions, like whether a move is broad market noise or specific to one security, which makes the portfolio agent feel thoughtful instead of mechanical. That is the real payoff here: we give the system a way to turn static holdings into a living picture, and that picture becomes the bridge to better analysis, better guardrails, and better decisions.
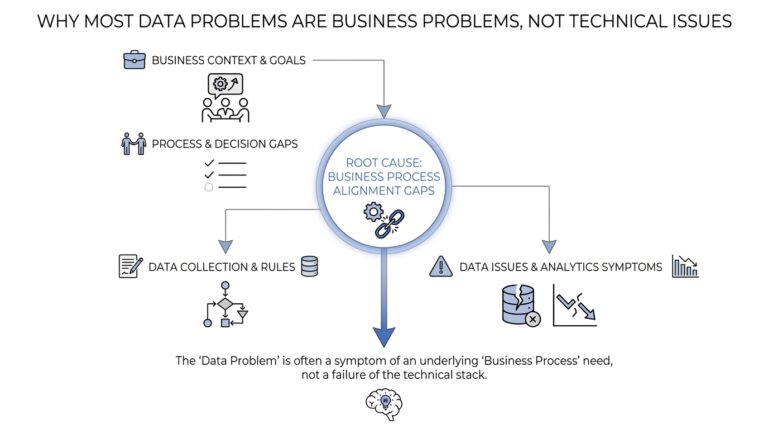
Evaluate Risk Signals
Now that the portfolio agent has fresh market data in hand, the next task is not to look harder—it is to look wiser. This is where we evaluate risk signals, which means turning prices, positions, and timestamps into clues about whether the portfolio is drifting into trouble. The agent is no longer asking, “What do we own?” It is asking, “What does this mix of holdings mean for volatility, concentration, liquidity, and possible loss?” In portfolio construction, those are all recognized risk measures, and practical risk limits often include concentration by security or sector, leverage, illiquidity, and formal measures such as volatility, drawdown, and value at risk (VaR), which estimates a modeled loss threshold over a given period.
The first signal we usually want to catch is concentration risk, because it has a sneaky way of growing in plain sight. A position can become too large not only because we bought too much of it, but because it performed well while everything else lagged, or because several holdings quietly point to the same company, sector, region, or theme. FINRA describes concentration risk as amplified losses that can happen when a large share of a portfolio sits in one investment, asset class, or market segment, and it notes that correlated holdings can create the same problem even when the names look different on the surface. That is why the portfolio agent should look through layers of ownership and not stop at the ticker on the screen.
Then comes liquidity risk, which is really the question of how easily we can get out of a position without making the price worse. Investor.gov defines liquidity risk as the risk that investors won’t find a market for their securities when they need one, and FINRA adds that liquidity gets harder when buyers and sellers are out of balance or when price volatility is high. For a portfolio agent, this means a position is not “safe” just because it is profitable on paper; if it is thinly traded, a rushed exit can create delay, slippage, or a much lower realized price than expected. So when the agent sees a large holding in an illiquid security, it should treat that as a risk signal, not a footnote.
Volatility is the next clue, and it helps to think of it as the bumpiness of the ride rather than the destination itself. FINRA explains that volatility is the up-and-down movement of market prices, and that more dramatic swings mean higher potential risk; it also notes that volatility can be especially uncomfortable for people who need short-term cash. In a portfolio agent, we use that signal to separate normal noise from something more serious. If volatility rises while the portfolio is already near its risk budget, or if drawdown is deepening, the agent should slow down and recheck assumptions instead of treating every price move as a fresh opportunity.
What risk signals should a portfolio agent watch first? The best answer is the one that connects exposure, exitability, and pain. If a holding is too concentrated, too hard to sell, or already contributing to a larger drawdown than the user can tolerate, the agent should raise its internal confidence threshold and ask whether the evidence really supports action. That does not mean the agent panics; it means it behaves like a careful co-pilot, noticing when the road gets rough and choosing whether to warn, rebalance, or wait for cleaner data.
Design Rebalancing Logic
Now that our portfolio agent can spot risk signals, we can let it decide what to do with them. That decision lives in the rebalancing logic, the part of the system that turns a drifting portfolio back toward its intended shape. In plain language, portfolio rebalancing means selling some positions, buying others, or doing nothing when the portfolio is still close enough to target. What should a portfolio agent do when weights drift? It should compare the current mix against the desired mix, measure the gap, and then act only when the difference is big enough to matter.
The first step is to define what “close enough” means, because every intelligent portfolio agent needs a clear boundary before it can move money. A target weight is the percentage of the portfolio assigned to a holding or asset class, and a tolerance band is the allowed amount of drift before the system intervenes. Think of it like a thermostat: if the room slips only a degree or two, we do not start a full heating cycle, but if the gap grows wider, we respond. That same idea keeps the portfolio agent from overtrading, which matters because frequent trades can create costs, taxes, and unnecessary noise.
Once we know the target and the tolerance, the agent can ask a simple but powerful question: is the portfolio still within policy, or has it wandered far enough to justify action? This is where the rebalancing logic becomes more than a math problem. It has to weigh the size of the drift, the importance of the asset, the current risk signals, and the cost of trading. A small deviation in a stable, low-risk holding may not deserve a trade, while the same deviation in a concentrated, volatile position may deserve immediate attention. That judgment is what makes a portfolio agent feel thoughtful instead of mechanical.
The next layer is choosing the trigger. Some systems rebalance on a schedule, such as monthly or quarterly, while others use threshold-based rebalancing, which means they wait until a position moves outside its tolerance band. The most useful portfolio rebalancing often blends both approaches, because time-based checks keep the portfolio from drifting silently and threshold checks prevent needless churn. In a portfolio agent, that hybrid design gives us a practical rhythm: we review regularly, but we only trade when the evidence says the portfolio truly needs it.
From there, the agent needs a sizing rule, which is the method it uses to decide how much to trade. This is where the portfolio agent moves from judgment to execution, and the details matter. It might trim only the excess above target, scale positions proportionally, or prioritize the largest risk contributors first. If one holding has grown too large and also raises concentration risk, the agent should not treat it the same way it treats a tiny, low-impact drift. The rebalancing logic should preserve the portfolio’s intent while respecting the realities of market impact and transaction cost.
We also need guardrails, because a portfolio agent should not rebalance itself into a problem. Before placing any order, the system should check cash availability, trade feasibility, market hours, and whether the proposed move would push the portfolio into a worse state somewhere else. It should also know when to pause. If prices are stale, liquidity is thin, or the data looks inconsistent with the holdings layer, the safest move may be to wait and explain why. That restraint is not hesitation; it is a sign that the workflow understands the difference between having enough information and having too little.
The best rebalancing logic also explains itself in human terms. When the agent proposes a change, it should be able to say what drift it saw, why that drift mattered, and what trade-off came with the recommendation. That explanation helps the user trust the system because they can see the reasoning instead of a black-box answer. In other words, good portfolio rebalancing is not only about restoring balance; it is about making each step understandable, defensible, and aligned with the portfolio agent’s objectives before we move on to execution and monitoring.
Add Safety Checks
Before the portfolio agent ever places an order, we need one more layer between intent and action. This is where safety checks step in, acting like the seatbelt and dashboard lights of the agentic workflow. They keep a confident-sounding model from moving too fast, using stale inputs, or treating an uncertain answer as if it were a settled fact. In a portfolio agent, that matters because the cost of a bad move is not just a wrong sentence; it can be a real loss, a compliance problem, or an explanation the user cannot trust.
The first safety check is data validity, because an agent can only reason well when the inputs are still alive. If a quote is stale, a holdings file is incomplete, or an identifier does not match the security master, the portfolio agent should stop and flag the issue rather than fill in the blanks with guesswork. What happens if the data feed is stale or the model gets too confident? The answer should be a deliberate pause, not a polished hallucination. This is the quiet discipline that keeps an agentic workflow honest: verify the source, confirm the timestamp, and make sure the record that triggered the decision is the same record the decision will affect.
Next comes policy validation, which is the system’s way of asking, “Is this action allowed?” A policy is a rule the portfolio agent must follow, such as a risk limit, an approval threshold, or a restriction on certain assets. These checks work best when they happen before execution, because they prevent the agent from suggesting something clever that still breaks the user’s rules. If a proposed trade would exceed concentration limits, violate a cash constraint, or push the portfolio outside the user’s stated tolerance, the agent should treat that as a hard stop, not a minor warning.
Confidence gating is the next layer, and it helps the portfolio agent know when to speak carefully. Confidence, in this context, means how strongly the system believes its own conclusion based on the evidence it has. That is useful, but it can become dangerous if the model treats uncertainty like a rounding error. A good safety check asks whether the evidence is strong enough to support action, and if not, the agent should ask for more information, narrow the recommendation, or switch from a trade proposal to a plain explanation.
We also want anomaly checks, which are designed to catch numbers that look technically possible but feel out of place. A position that jumps sharply without a matching market event, a balance that does not reconcile, or a suggested order that is far larger than the portfolio context all deserve attention. Think of this like noticing that one puzzle piece has the wrong shape: it may not prove anything by itself, but it tells us to slow down and inspect the full picture. In an intelligent portfolio agent, anomaly detection is one of the most practical guardrails because it keeps small data mistakes from turning into confident action.
Approval gates add another kind of protection, especially when the workflow crosses from analysis into execution. An approval gate is a checkpoint where the system must wait for a user, supervisor, or automated rule to authorize the next step. This is especially valuable when a recommendation is high impact, when the portfolio agent is uncertain, or when the action would change the user’s exposure in a meaningful way. Instead of pretending every decision belongs to the model, we let the workflow distinguish between suggesting, preparing, and actually acting.
The best safety checks also include a fallback path, because safe systems need a graceful way to say no. If the agent cannot verify the data, cannot confirm the policy, or cannot justify the trade with enough evidence, it should fall back to a safer response such as asking a clarifying question, summarizing the uncertainty, or recommending no action for now. That restraint is not a sign of weakness; it is what makes the portfolio agent dependable. When we build these checks into the agentic workflow, we are not slowing the system down for no reason. We are making sure every step can survive scrutiny before we trust it with the portfolio.